The Ultimate Guide to Advanced Persistent Threat Protection
A curated Kiwi edition of TechDay news, analysis, interviews, reviews, job moves, and related resources for Advanced Persistent Threat Protection.
What to know about Advanced Persistent Threat Protection
Advanced Persistent Threat (APT) Protection is a crucial aspect of modern cybersecurity focused on defending against prolonged and targeted cyberattacks that aim to compromise sensitive systems while evading typical defenses. Such threats often involve sophisticated methodologies that allow attackers to maintain access over extended periods, posing significant risks to organisations' critical data and operations.
Exploring the latest stories tagged with Advanced Persistent Threat Protection reveals evolving challenges and responses in this domain. From rising state-sponsored activities, advanced malware campaigns, to innovations in artificial intelligence boosting both attacks and defenses, the landscape is rapidly shifting. Readers will gain insights into strategic collaborations, technology advancements like AI-driven detection, and legislative movements aimed at strengthening cyber resilience against persistent threats.
For organisations, security teams, and individuals seeking to understand and keep pace with these advanced persistent threats, this collection offers timely analysis, expert perspectives, and practical guidance. Engaging with these stories supports a deeper comprehension of threat mechanisms and the evolving tools and partnerships designed to thwart them, emphasizing the vital role of vigilance and adaptive security strategies in today's digital world.
Kiwi Advanced Persistent Threat Protection News
Regional stories with direct local relevance
Fewer New Zealanders harmed by cyber attacks, survey finds
Greater use of two-factor authentication and password managers has helped cut the share of adults reporting cyber harm to 27% from 36%.

WitFoo opens 100 million-record cyber attack dataset
Researchers can now train on live attack traffic after a new open-source dataset adds 100 million labelled security records from production systems.

Datacom finds New Zealand firms lack cyber recovery plans
Only 30% of New Zealand organisations have a cyber recovery plan, leaving customers and operations exposed if attacks cause prolonged outages.

Give to gain: How sponsoring women strengthens national security
Sponsoring women into senior cyber roles is emerging as a strategic lever to plug talent gaps and bolster New Zealand's national security.

Automating the repeatable, humanising the exceptional: Delivering real AI value with an ontology‑led approach
Lancom champions an ontology‑led AI approach, automating repeatable tasks while elevating human expertise to deliver real business value.

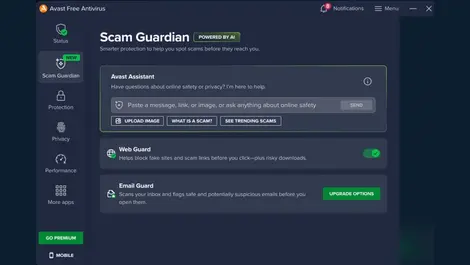
Norton launches Genie scam-check tool in ChatGPT NZ
Norton debuts Genie scam-check app inside ChatGPT for New Zealand users, flagging risky emails, texts and links in everyday chats.
Analyst Insights
Research and market analysis connected to Advanced Persistent Threat Protection
Cognizant launches Secure AI Services for enterprises

Group-IB named a Leader in Gartner cyberthreat report

CrowdStrike leads Gartner cyberthreat intelligence quadrant

Check Point wins Frost & Sullivan recognition for WAF

Check Point tops Miercom hybrid mesh security benchmark
Featured News

HPE assisting IT teams navigate complex challenges
HPE Networking says AI, zero trust and SASE are reshaping network security as remote work and connected devices make threats harder to control.

Yubico well-prepared for post-quantum computing threats
Businesses are racing to upgrade defences as Yubico says quantum computers could expose banking, health data and other records within years.

Upwind Expands to Sydney: Real Time Cloud Security for APJ
The Sydney move follows a USD $250 million funding round as the cloud security firm bets on real-time protection for fast-growing AI workloads.

Google flags urgency as AI reshapes cyber threats
Patching delays now carry greater risk as Google says AI is helping attackers scale intrusions, speed up breaches and automate operations.

Exclusive: Google Cloud on the road to autonomous SecOps
The new tools could cut analysts’ manual threat-response work from days to minutes as Google Cloud pushes SecOps towards an autonomous SOC.

Netskope's Tony Burnside - visibility is key to AI security
AI tools are creating hidden east-west traffic that security teams struggle to monitor, raising the risk of data leakage and compromise.

Exclusive: Celonis global banking head says AI rollout hinges on process intelligence
Banks risk wasting AI spending unless they first map how work really flows, as Celonis says process intelligence is becoming phase zero.

TrendAI: Evolving the cybersecurity value proposition
New research shows two-thirds of Australian business and IT leaders feel pressured to approve AI projects while overlooking security risks.

Rockwell Automation brings SecureOT to industrial systems
Australian operators face rising cyber risk as Rockwell warns poor visibility and unmanaged remote access can disrupt safety-critical systems.
Reviews
Expert Columns

Why service desks are emerging as a critical security weakness

Stolen credentials don't have to mean a breach

Turning security into a story: How managed service providers use reporting to drive retention and revenue

How MH Enterprise turns trust into cybersecurity success

Small alert, big defense: Inside a SOC's early-morning response

Don't be fooled: The SaaS label that's misleading your security team

Why AI-powered security needs network telemetry across the hybrid cloud

From fragmentation to focus: Can one security framework simplify compliance?

Saving the weekend: How SonicWall's SonicSentry SOC stopped a Saturday night cyberattack

Upgrade advantage: Future-proofing for partners, MSPs and MSSPs
Interviews
Interviews and video coverage from the networkRecent Advanced Persistent Threat Protection News

Government orders review into ManageMyHealth data breach
Government orders urgent review into ManageMyHealth cyber breach as hackers threaten to leak 400,000 patient files over NZD $60,000.

NZ cyber losses more than double amid email scams
New Zealand cyber losses hit NZD $12.4 million in Q3 2025, more than doubling as business email scams and high-value transfers surge.
New Zealand issues mass alert over Lumma malware risk
New Zealand cyber agency emails 26,000 people in first mass alert over Lumma Stealer malware infecting Windows devices nationwide.

Productivity gains from AI will stall unless New Zealand fixes its security foundations
New Zealand's AI productivity promise will falter unless firms simplify systems, curb shadow AI and strengthen cybersecurity foundations.

New Zealand urged to boost cyber security as threats diversify
New Zealand organisations face growing cyber threats from state actors and criminals, urged to strengthen defences as attacks target all sizes and sectors.

Hidden cyberattacks & ransom threats rising for NZ businesses
Most cyberattacks on New Zealand businesses go unreported, with NSP warning ransom payments are more common than widely known, exposing firms to hidden risks.

New Zealand cyber defence firm wins top award amid daily attacks
New Zealand's cybersecurity firm DEFEND clinched Microsoft's Global Security Partner of the Year amid rising state-backed cyber attacks targeting local businesses daily.

DEFEND wins global Microsoft award as cyber threats surge in NZ
New Zealand cybersecurity firm DEFEND wins Microsoft's Global Security Partner of the Year amid rising cyber threats to public and private sectors.

Why NZ Businesses Must Get Serious About Cybersecurity
New Zealand firms face rising cyber risks as attackers exploit weak controls; experts urge urgent steps to boost defences and test incident plans.

AI drives smarter, converged cybersecurity across New Zealand
Nearly all large New Zealand firms now use AI in cybersecurity, shifting to smarter, automated defences amid growing cyber threats and evolving risks.

New Zealand's best in cybersecurity honoured at 2025 iSANZ Awards
New Zealand's top cybersecurity experts and organisations were honoured at the 2025 iSANZ Awards amid rising cybercrime losses of NZD $1.6 billion annually.

Cyber risk tops Pacific business concerns amid growing climate threat
Cyber threats top concerns for Pacific businesses in 2025, as economic and climate risks rise, according to Aon's Global Risk Management Survey.

Norton expands AI scam protection to New Zealand & globally
Norton has extended its AI-powered scam protection to New Zealand and globally, boosting defences across web, email, SMS, videos, and calls for all Norton users.

Lisa Fong steps down as NCSC chief after 13 years of service
Lisa Fong has resigned as head of New Zealand's National Cyber Security Centre after 13 years, leaving a strengthened agency and legacy.

Extortion and ransomware drive over half of cyberattacks
Over half of cyberattacks last year were driven by extortion or ransomware, with criminals focusing on financial gain rather than espionage, Microsoft reveals.

New Zealand businesses urged to boost security against rising cyber threats
New Zealand's intelligence chief warns rising foreign cyber espionage demands businesses strengthen security to protect innovation and national interests.

Kordia appoints Willo Chapman Head of Sales for cyber & cloud
Kordia has appointed Willo Chapman as Head of Sales for Cyber, Cloud and Connectivity to drive digital services growth and customer success in New Zealand.

Insider threats: Protecting what matters most from within
Insider threats cost organisations USD $17.4 million annually; Gallagher Security urges a people-first approach to protect assets from within.

AI gives cyber criminals new tools in evolving ransomware threat
Cyber criminals are increasingly using AI tools to enhance ransomware attacks, complicating defences for individuals and organisations alike.

Most NZ government bodies not ready for strict email security law
Three-quarters of New Zealand government bodies lack the highest email security standard required by upcoming October 2025 regulations, research finds.
.webp)
