
Beyond espionage – how the Lazarus Group is reshaping cybersecurity threats
Fri, 16th Aug 2024
Meet the Lazarus Group, also known as Hidden Cobra. The group is a notorious cybercriminal organisation believed to be backed by North Korea. It first came onto the scene in 2009 and, over the years, has become infamous for its highly sophisticated and destructive cyberattacks, primarily aimed at espionage, sabotage and financial gain. Whether its spying on sensitive information, wreaking havoc on systems or swiping massive amounts of money, its global trail of high-profile hits showcases both its scale and reach.
Time-lapse: then and now
The Lazarus Group is widely reported to be associated with the North Korean government, specifically its reconnaissance bureaus which are tasked with cyber warfare and intelligence gathering. The group's activities align with North Korea's geopolitical and economic objectives, often targeting entities that could provide financial or strategic benefits to the regime.
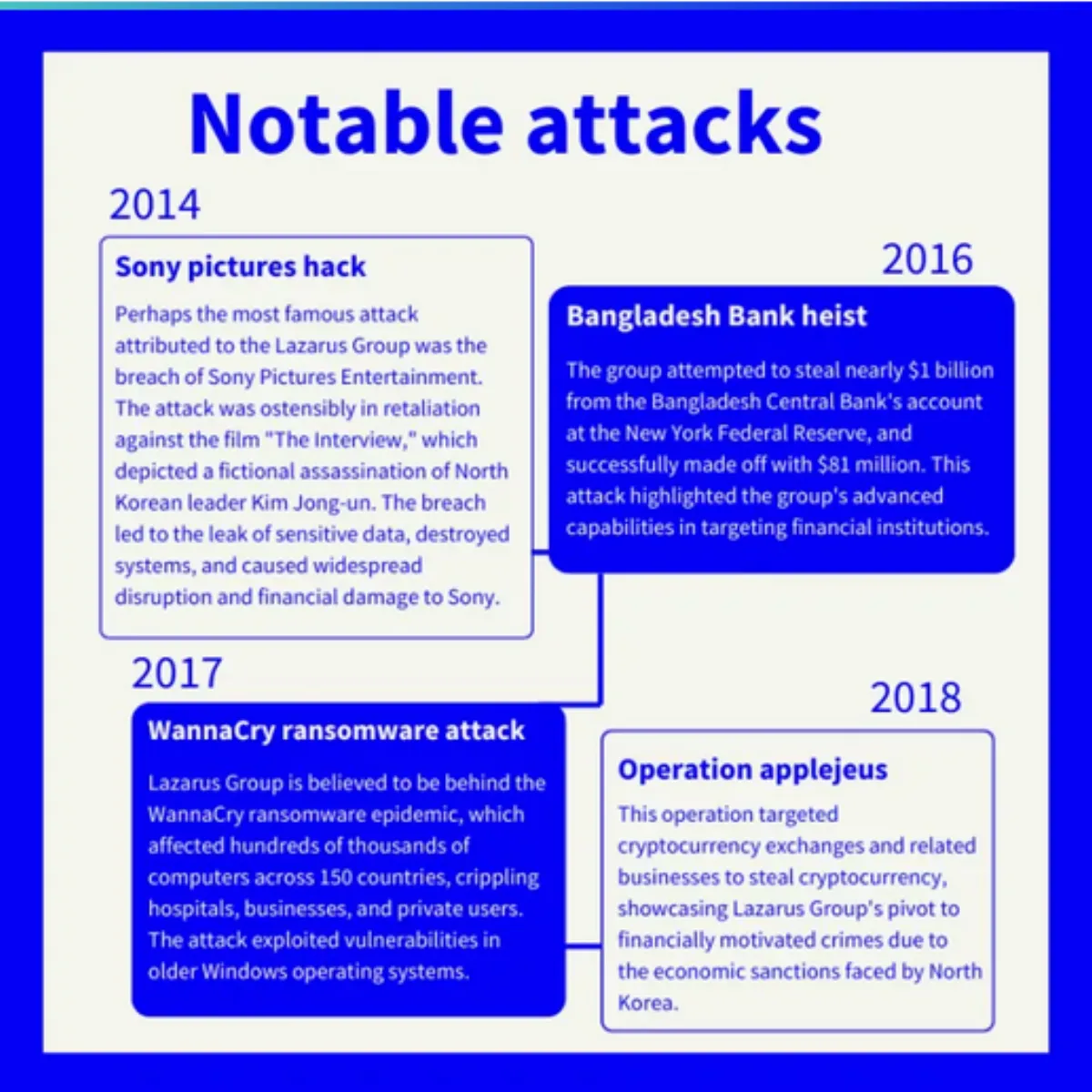
Initially the group focused on espionage-type activities (snooping around for sensitive information), typical of Advanced Persistent Threats (APTs). But as time passed, its focus shifted towards bringing in money. Through intricate attacks on the bank and cryptocurrency markets, the group has devised complex "virtual" heists. This shift is most likely driven by the need to secure foreign currency for the North Korean regime amidst global sanctions. The evolution from spies to cyber-thieves underscores its adaptability and relentless pursuit of financial gain.
Evolution, adaptation and techniques
Lazarus has managed to stay ahead in the cyber arms race by continually evolving its methods and tools. It leverages zero-day vulnerabilities – undisclosed bugs in software that can be exploited to gain unauthorised access or cause harm. These vulnerabilities are highly prized on the black market and can be used to target very specific groups or individuals, thereby minimising detection and maximising attack success.
The group has been reported to target individuals with fake job opportunities, particularly in the tech and crypto sectors. This strategy not only allows it to steal valuable cryptocurrency assets but also potentially gives insider access to crypto exchanges and tech companies, further enabling espionage and financial theft.
The latest find: Lazarus is setting its sights on freelance developers working on NFT and crypto-wallet projects. It is using various platforms to distribute malicious JavaScript, including the popular freelance site "freelancer.com" to find developers involved in NFT projects. Additionally, the Lazarus Group has exploited GitHub repositories and Google Cloud services to spread its harmful scripts, sometimes posing as potential employers or interviewers to lure victims.
The focus on individuals through tactics like fake job interviews marks a significant shift in Lazarus Group's strategy, indicating that no one is off-limits.
Global impact – evolving tactics and how to combat them
The actions of the Lazarus Group have significant implications for international cybersecurity and economic stability. Its campaigns demonstrate the capabilities and intent of state-sponsored actors to disrupt, steal or sabotage, highlighting the importance of robust cybersecurity practices at all levels – from governmental to personal.
Understanding groups like the Lazarus Group helps in developing more effective defences and strategies to counter such advanced threats, safeguarding critical information and financial assets globally.
The role of Gen
Gen and its family of consumer brands play a crucial role in identifying and mitigating threats from groups like Lazarus. By detecting zero-day exploits and other attack vectors used by these groups, security firms can neutralise the tools at the disposal of attackers, thereby increasing the cost and difficulty of their operations. This helps to keep high-level threats focused on larger targets rather than everyday users.
Challenges and strategies for cybersecurity experts
Combating nation-state actors like Lazarus is challenging due to its state backing, significant resources and high skill level. The key to defence lies in relentless vigilance – constantly improving defensive technologies, sharing threat intelligence within the cybersecurity community and maintaining rigorous cyber hygiene practices.
International cooperation is vital in the fight against APTs like Lazarus. Sharing intelligence across borders and among private cybersecurity entities can help in forming a unified defence against common adversaries, ensuring broader protection against these sophisticated threats.
Anticipate and prepare
As cyber tactics continue to evolve, so will the strategies employed by the Lazarus Group. Anticipating and preparing for future methods, likely more sophisticated and covert, is essential for staying ahead of threats. By understanding Lazarus Group's tactics and continuously enhancing our defences, we can hope to safeguard our digital lives against these formidable adversaries. Both companies and individuals must remain vigilant, educated and prepared to tackle these advanced threats head-on.
International collaboration and proactive security measures will be our best tools in this ongoing battle to build a more secure digital future, keeping one step ahead of those who seek to disrupt and exploit our interconnected world.