You don't have to look at many data breach reports to get a sense that stolen user credentials can be the keys to the kingdom for determined attackers. We spoke to RSA's Craig Dore about why passwords aren't the best solution, and why multifactor authentication (MFA) is a much better choice for businesses.
What are some of the difficulties and security risks surrounding the use of a single form of authentication, like a password or PIN?
Securing business applications is always about balancing user convenience with security. Passwords are a default with respect to identifying the user and keeping unwanted individuals from accessing the application.
They are also well understood by users and 'easy' for system owners because the functionality is generally already built into most applications.
However, there are many downsides to passwords and PINs. Today's users typically need to manage (and remember) passwords for many applications that they use in both their personal and professional lives. Most of these applications have varying requirements for passwords – some will reject new passwords if they do not have a number or symbol – or even worse, it might not allow one at all!
Multiply this problem by the number of online services that you might use and you'll quickly realise that passwords are no longer easy.
Passwords can be guessed, hacked, stolen, shared, or some users might even be tricked into handing them over. It is even worse when you consider how often users re-use the same password across different applications, and how many password databases have been stolen by hackers over the last decade.
When you consider the number of different ways that passwords can be circumvented or even defeated, I think it is fair to say that the password is an outdated technology. In this day and age, businesses need to invest in a solution that can provide an alternative to passwords, but also provides user convenience.
What other forms of authentication could businesses use?
In general, strong authentication is referred to as "two-factor authentication" (2FA) or "multi-factor authentication" (MFA). These concepts are effectively the same thing. The idea is that the application is protected with more than "one factor" (aka a password) and combines two or more additional factors such as "something you know", "something you have" or even "something you are" (such as a biometric).
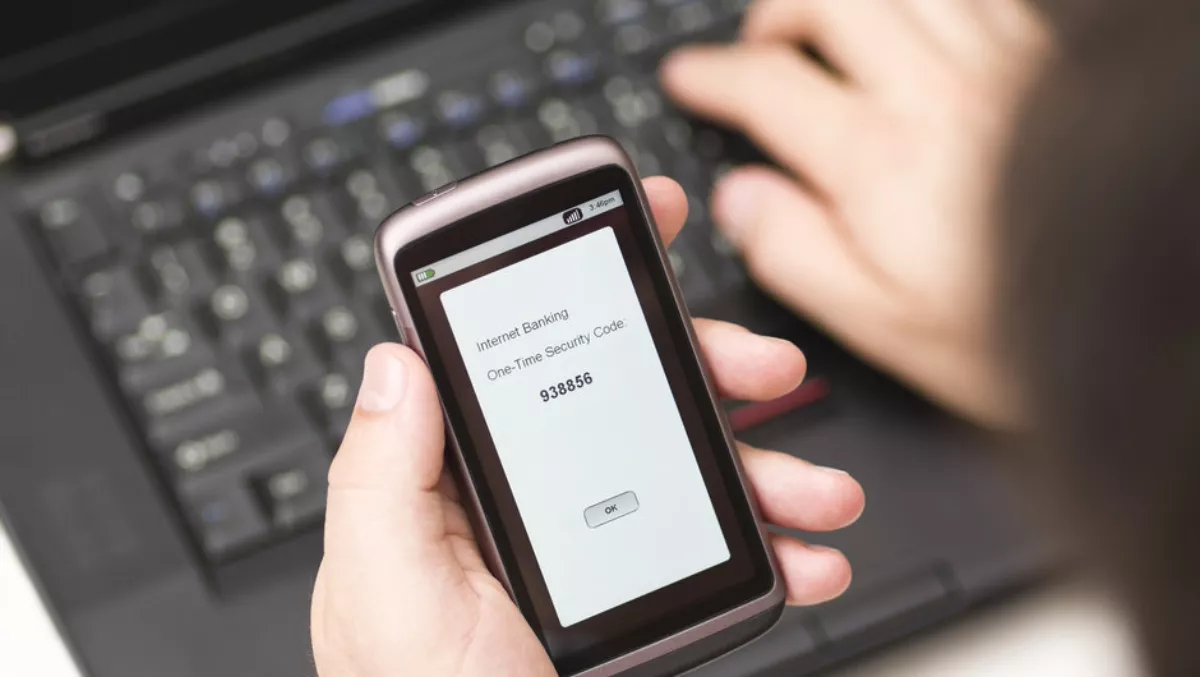
One of the most popular authentication solutions utilises a set of numbers that are sent over a SMS message to the user's mobile phone to provide a "second-factor" in addition to a password to gain access. However, the reality is that even the SMS network can be exploited. For example, the very popular Internet site Reddit was breached using a technique called SIM swapping.
There are other, more secure alternatives though. Popular forms include:
- A set of numbers that are generated within the application (called a "token" or "one-time password")
- A push notification where the user is sent a message to the app on their phone to which the user can respond to by tapping a "Yes" or "No". This technique does NOT use the SMS network but is an Internet-based message sent directly to the smartphone app
- A biometric, like your fingerprint or face recognition (such as Apple's FaceID or Samsung's Face Recognition)
Furthermore, there are many solutions out there that provide a dedicated hardware device that displays an ever-rolling set of numbers, which the user has to type into the protected application.
This is very secure because the device is air-gapped, meaning it is not connected to the Internet or another network. Instead, the numbers (the "token code") are generated using a time-based algorithm.
This solution isn't great from a user perspective as it is cumbersome, but are sometimes required, especially when working in locations where phones aren't allowed, like data centers.
In general the smartphone and hardware-based examples are much harder to exploit, but they require some amount of additional management to properly implement in an organisation.
In the consumer market, there are hardware devices that support a popular standard called "FIDO" (Fast Identity Online) which allow users to connect that device to their PC or Phone. Pushing a button on the device provides the second-factor authentication needed to access the application.
Security platforms that provide strong authentication should support the FIDO standard, so always be sure to ask if they do. Ideally you would combine this type of token with another form-factor such as a smartphone-based token or other methods. Another good thing to check as it increases the security for users like IT administrators or other critical personnel.
Could you provide practical examples of how MFA could work for a business?
There are many practical examples of how MFA would work for a business. Typically, businesses have a range of applications that might live inside of their premises or out in the cloud.
A good MFA solution would cover access for both types of applications, and enable access for both employees and third parties such as contractors. As a way to offer both security and convenience, an MFA platform should allow users to log into applications using their fingerprint on their smartphone.
And when it comes to users accessing applications or data of a sensitive nature, an MFA platform would ideally challenge users with more than one form of authentication based on different and separated physical channels – say a smartphone method combined with a hardware device. These two forms are then evaluated together during the access request.
When evaluating an MFA platform, you need to also consider overall system ownership and management overhead. Ideally you would use a solution that provided as much automation and user-level self-service as possible.
How could MFA be applied to cover company-owned devices in the office and employees' bring-your-own-device (BYOD)?
There are varying philosophies in relation to whether a MFA platform should provide some measure of device inspection to ensure that the device is safe to use, for example, ensuring that there is no malware on the device.
I believe that it is absolutely essential that "rooted" phones not be permitted to be used as an authenticator. Also being able to plug into an existing Mobile Device Management (MDM) platform would be highly desirable, although the MFA solution should not attempt to replicate the great features of those platforms.
Let the MDM solution focus on what it does. Ideally, MFA platforms should incorporate the "something you know" piece of the factors that are evaluated during an access request, and automatically prevent repeated attempts to guess that factor. Flexibility is key to supporting both approaches!
How do you balance ease of use and convenience with strong MFA? Is it possible?
With the rise in BYOD, a good MFA platform allows a user to register their MFA smartphone application or hardware-based authenticator without helpdesk involvement.
Best practice would mean that a fingerprint or push notification isn't considered the absolute best proof of a user's identity. Instead, these authentication methods should be married to another dimension relating to user access - their behaviour over time.
Take for example, a user logging into the same application at the same time of day, from the same device from within the corporate network every week day. A system that could silently take this into account automatically is a "smart" authentication platform.
Such a "smart" system would not bother the user with a MFA challenge every time they logged in following this pattern. Only when the user deviates from this established behavioural pattern, the platform would automatically detect this and challenge the user accordingly. This can be best described as a "risk-based" or "adaptive" authentication platform.
Utilising a platform that combines easy and convenient authentication methods with risk-based technology is the ideal marriage between convenience and good security.
Multi-factor authentication is often cloud-based. What do organisations have to consider?
Many Australian and New Zealand organisations in public and prudential sectors are regulated by privacy and "data sovereignty" legislation.
The Australian Privacy Principles (APPs) are one such example. In terms of where security solutions are provided, these types of organisations must prioritise "on-shore" or "near-shore" when evaluating public or private cloud platforms, particularly for security services. Applying for exceptions to the relevant Commonwealth Commissioner can be a lengthy and onerous process.
Thus, leveraging the scalability and elasticity of cloud-based platforms and infrastructure is restricted, despite legitimate benefits of doing so. My advice is to carefully consider where a cloud-based service is hosted. RSA provides an Australian-hosted authentication cloud platform that is housed in a certified "protected level" government facility in Canberra.
What advice would you give to organisations that believe MFA is 'nice to have but not necessary'?
We often see this out in the business world. One of my first questions is "do you use passwords to access any of your systems, applications or data?" Generally, the answer is yes. If that is the case, I would say that organisation is automatically at risk and should absolutely consider elevating the priority of MFA within their day-to-day operations.
What would you suggest as the first step for organisations that want to investigate stronger authentication for their business?
The best suggestion is to not "boil the ocean" with respect to the technology. Start small and address the most critical applications and users first. An easy question to ask yourself is, "Are there any business processes in our organisation supported by applications that are only protected by passwords, and if they were breached, would this essentially stop us from operating our business?
RSA is offering you an exclusive look at MFA security in its white paper titled How multifactor authentication is the new bare minimum for good security hygiene.