Dimension Data showcases APAC threat landscape at exclusive Auckland event
Fri, 23rd Jun 2017
NTT Security's Global Threat Intelligence report has firmly warned organisations that entertaining cybersecurity 'for the sake of doing security things' is a grave mistake; and businesses will get caught if they limit it to being just an IT problem.
The report, which featured findings from 6 billion attempted attacks and trillions of security logs over the past year, found that phishing attacks are prevalent and are responsible for as much as 73% of malware being delivered to organisations.
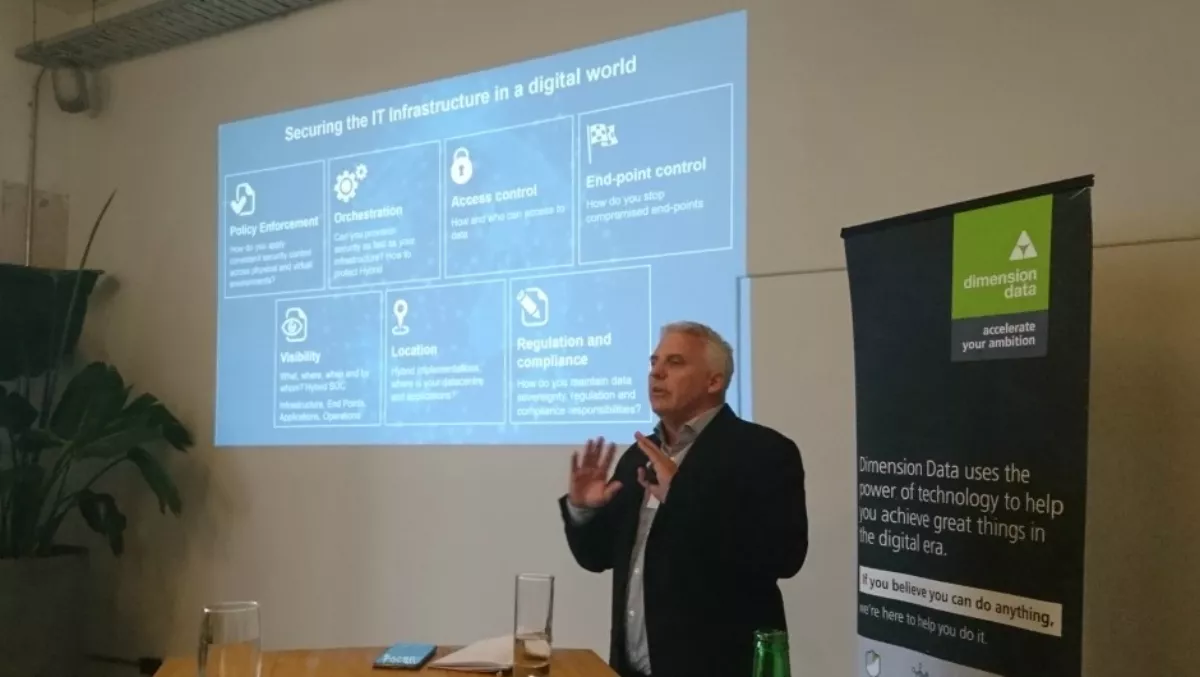
Yesterday Dimension Data held a small event in Auckland surrounding the release of the report, in which the company highlighted how the report was relevant to New Zealand organisations.
Opened by Dimension Data's security business unit lead Tony Jenkins, the event included commentary from Dimension data Group cyber security strategist Mark Thomas and Neville Burdan, general manager of Dimension Data Asia Pacific.
Thomas took the audience through the NTT Security report. He explained that the top trends include phishing, social engineering and ransomware. Business email compromise fraud, IoT and DDoS attacks are going after businesses and end user applications.
APAC a testing ground for phishing attacks
Thomas says that APAC is a testing ground for phishing attacks because it is heavily invested in security technologies. If malware works here, it will work anywhere.
"Asia is a hotbed for being attacked because it has perimeter security," Burdan adds.
In particular, New Zealand security teams sit inside IT and report to the IT operations manager - a concerning prospect that siloes security as being an IT problem, not a business wide problem. Dimension Data says that security decisions must be business decisions.
DDoS and IoT - major areas of concern
"Analysts have been talking about IoT deployment for some time. We haven't seen massive adoption to date but organisations that have are seeing multiple DDoS attacks. They're not architecting IoT into the network correctly, and not configuring it right," Thomas says.
In Australia, DDoS attacks account for 24% of all attacks. In Asia, they account for 16%. Thomas attributes this to the explosive growth in IoT.
New Zealand organisations face a lack of resources that have driven up the cost of labour, which means organisations can't afford large security teams. IT departments are looking for 'security bling' and automation but they haven't quite mastered the technologies.
Thomas explains that while attacks originate from US IP addresses, it doesn't mean attacks are coming from the US itself.
"Chinese don't like to attack directly, they like to use adjacent countries to direct their attacks," Thomas says.
Security vulnerabilities and patch management
The report found that organisations are ignoring patch management. Thomas says that 47% of vulnerabilities are more than 3 years old and 8% are more than 10 years old.
Conversely, the number of vulnerabilities being disclosed since 2013 has skyrocketed. The mismatch suggests there is a lack of skilled resources to roll out patches fast enough.
"We find New Zealand organisations tend to focus on OS patching but forget end-user applications such as Internet Explorer, Firefox, Java and Adobe. These are the applications hackers target most so we need to start to extend our patching regime to these areas," the company says in a statement.
Response plans and opportunities for businesses to harness MSSP expertise
In New Zealand, the report found that organisations are slowly maturing - but as of 2016, 68% of organisations have no formal response plan. This provides opportunities for managed security service providers (MSSPs) like Dimension data, as clients try to deal with the issues - and not just the technological ones.
"Many clients are reaching out to us because yes they've been compromised, but how do they respond?" Thomas explains.
"We have to start thinking about humans as an asset, and how do we secure that asset? What data are we sharing and how are we sharing that data with other third parties? It's a people, process, technology discussion."
Dimension Data: Future directions for security
Dimension Data, part of the $120 billion engine that it NTT Group, has built its business around four pillars: digital infrastructure, hybrid cloud, workspaces for tomorrow and cybersecurity.
According to Burdan, the company is driving security across all of these pillars.
"We're trying to move the discussion from siloed security into automated platform that can protect against attacks," he says.
"NZ is the number one adopter of Office 365. But how do we manage assets and protect our posture on and off our networks?"
While intelligence sharing will help organisations protect each other from threats, there are still issues such as what defines intelligence, how to get it and how to share it with other organisations.
"We need to extend the conversation from the back room to the boardroom to the living room, talking with family members and children. Everyone is using new types of devices. It's not just a corporate problem, it's a social problem as well," Thomas says.
Protection and detection controls
According to Burdan, Dimension Data focuses its services on assess-comply-manage-respond step process. For that purpose, the company has targeted its solutions across security advisory, compliance and architecting services.
The company has also taken a layered approach to security by mapping in architecture of major tier 1 security partners such as Fortinet, Symantec, Microsoft, Carbon Black, McAfee, Check Point, McAfee and others.
The company also provides managed security service in the areas of email, web gatewalls, firewalls, intrusion and detection and web SaaS.
The company's ultimate goal? To take the statistics from NTT Security and make sure they don't affect APAC businesses.
"We want to leverage the technologies that come from global but make it real here in New Zealand," Burdan concludes.