Deep web vs dark web: NortonLifeLock explains the difference
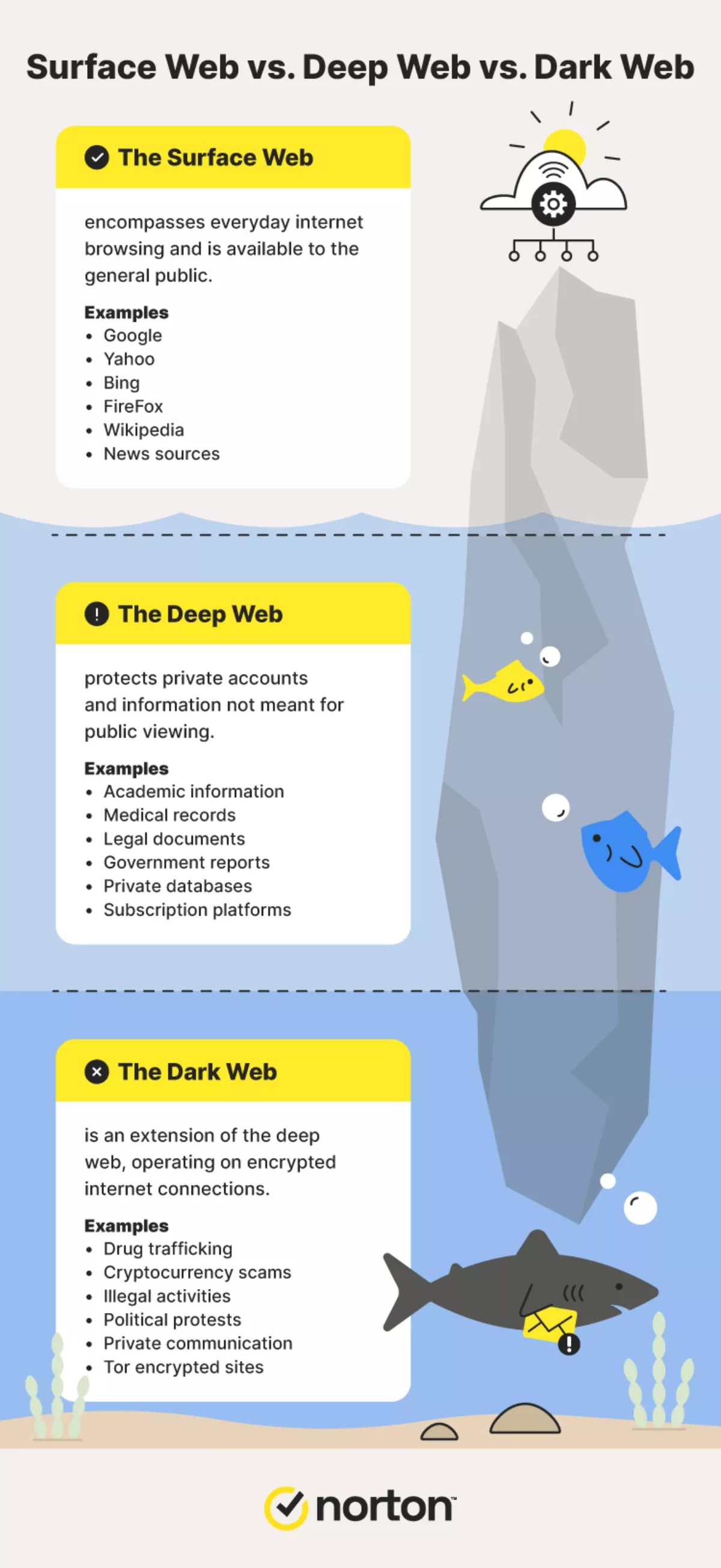
Like the world as we know it, the internet has a few layers to it. You might think of it as an iceberg floating in the middle of the Antarctic.
There's the surface web that most of us use or see every day, the deep web nestled right below, and then the dark web buried even further down. Deep web and dark web sites can have bad reputations, but that's partially because they're surrounded by so much mystery, leading to confusion and a trail of misinformation.
For more perspective, dive into the Norton breakdown of the deep web vs. the dark web, including the purpose of each and how they differ. You'll also find answers to frequently asked questions about deep and dark web websites.
What is the deep web?
Simply put, the deep web describes all web pages hidden from the search engines we use daily. Website owners do this to protect websites not meant for public viewing, like email and banking accounts, private social media pages, and electronic health records. The deep web works by requiring you to have a specific password or link that will give you access to the private site you're trying to enter. This way, prying eyes will run into trouble accessing your personal information.
Some mainstream sites are only accessible via the deep web because of how they customise each page to the user. Streaming platforms are a great example of this, requiring you to enter your login credentials immediately before you can continue to watch your beloved TV shows and movies.
What is the dark web?
The dark web is a more guarded subspace of the deep web, hosting encrypted websites for its users. However, these sites are only accessible with specific web browsers. People use this encrypted space as a means to help protect their identity and online privacy, but some hackers like to use these features to carry out illegal activities.
Some crimes that someone might come across include:
- Arms trafficking
- Drug trafficking
- Cryptocurrency scams
- NFT scams
- Phishing scams
- Espionage
- Sale of stolen credentials and data
With Tor Project and other similar dark web browsers, anyone can surf the dark web and communicate with others without having their IP address, search history, cache, or cookies tracked. These are unique search engines designed specifically for accessing the dark web. And contrary to what you may think, the dark web also hosts sites that aren't involved with illegal work.
What are the differences between the deep web vs. the dark web?
Now that you know what the deep and dark web are, seeing their differences may be a bit easier. But to ensure you have a clear picture, we've outlined them below.
Pros of the deep web vs. the dark web
In the digital age, almost everything has good and bad aspects.
Pros of the deep web include enhanced online privacy, more secure connections and password and/or link protected information. The pros of the dark web include no censorship and anonymous browsing.
Cons of the deep web vs. dark web
The deep web may be great for helping protect personal information, but that doesn't mean it's un-hackable. Cybercriminals often use tactics like credential stuffing and password spraying to get hold of the details needed to steal and/or expose your data.
Sure, the dark web offers a kind of anonymous browsing not available on the deep web or surface web, but there are even more threats you might encounter as you browse. Hackers use this domain to carry out illegal activities that could implicate you and your information if you stumble across the wrong site.
Deep web vs dark web FAQs
Is it illegal to access the deep web or the dark web?
No, it is not illegal to access either the deep web or the dark web.
What are the main dangers of the dark web?
There are several dangers present on the dark web, from child pornography and drug trafficking to illegal arms dealings and cryptocurrency scams.
What is Tor Project?
The Tor Browser is an encrypted network used for surfing the dark web. The level of encryption provides anonymous internet browsing for users.
Can Tor be traced?
The encrypted network the Tor Browser uses to access the dark web is very hard to trace.
What happens if you go on the dark web?
Those using the dark web disconnect from the public servers used for everyday online browsing and connect to a dark web browser that provides increased privacy and security.

