Cyber Smart Week takes cybersecurity back to basics
Thu, 21st Oct 2021
Sometimes cybersecurity advice can come across as a rehash of the same tired old rules, and for some, it breeds complacency. However, the seemingly never-ending torrent of advice is necessary to stem the never-ending deluge of cyber threats.
There is immense value in repetition - and for a good reason. Cybersecurity awareness is now a critical part of every business, small and large, right alongside accounting, HR, and primary business functions. And it's the critical nature of cybersecurity that drives the ongoing need for awareness and action.
Cyber Smart Week, led by CERT NZ to educate and empower New Zealand businesses and individuals to improve their cybersecurity, is a timely reminder that even small changes can make a big difference.
CERT NZ director Rob Pope says cyber attacks are becoming more sophisticated - and there are more of them than ever before. We're not just talking about the ones that get publicity, such as the Waikato DHB ransomware attack or the Air New Zealand data breach. Most cyber attacks stay out of the headlines, and some attacks are not detected until months or years later.
Pope notes that businesses in Aotearoa usually have tight security budgets, especially with the current economic uncertainty.
"The speed at which a software vulnerability can be transformed into a viable attack has significantly increased over the years, so the pressure is on businesses to get their software updated before they can be impacted."
Typically, small and medium businesses are the ones that are frequently targeted, he says. But when budgets are tight, there can be sacrifices.
"Often cybersecurity might seem like a line item organisations struggle to afford. We have seen businesses become more conscious of data privacy and security, and this has translated into a greater awareness of the need for cybersecurity within organisations, which is a good thing," Pope says.
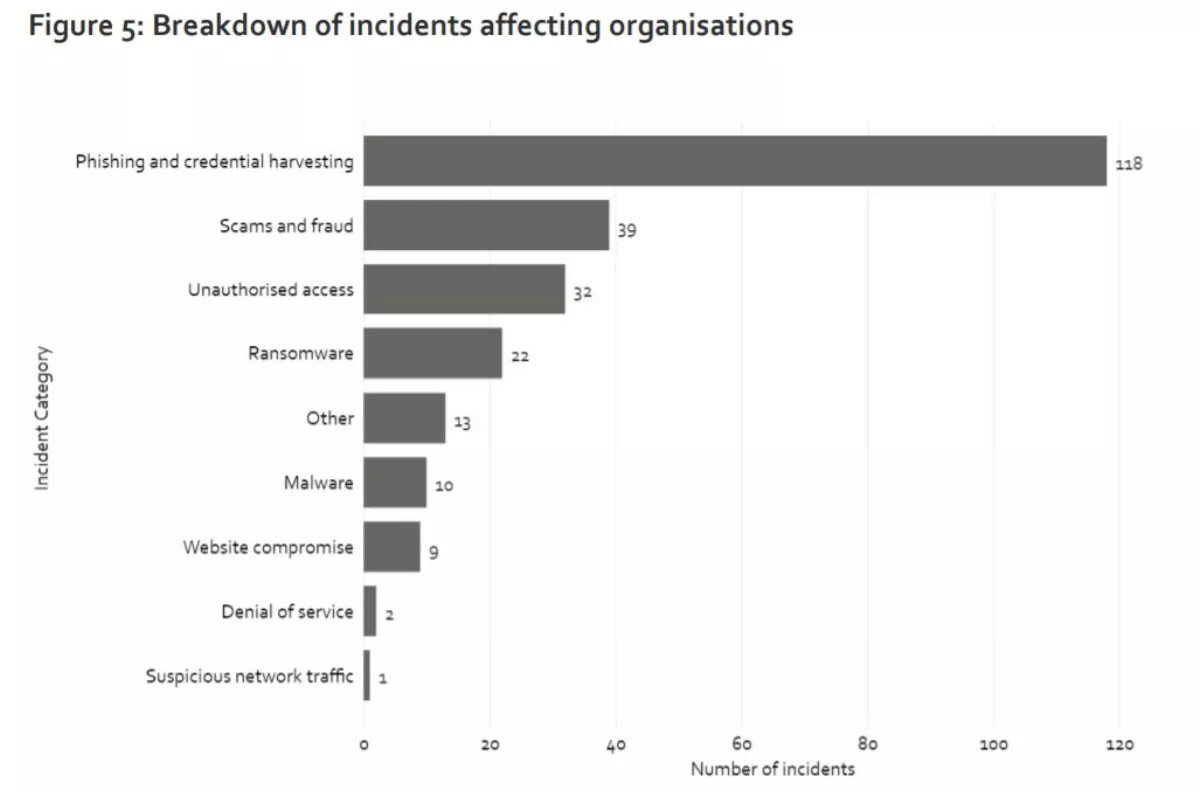
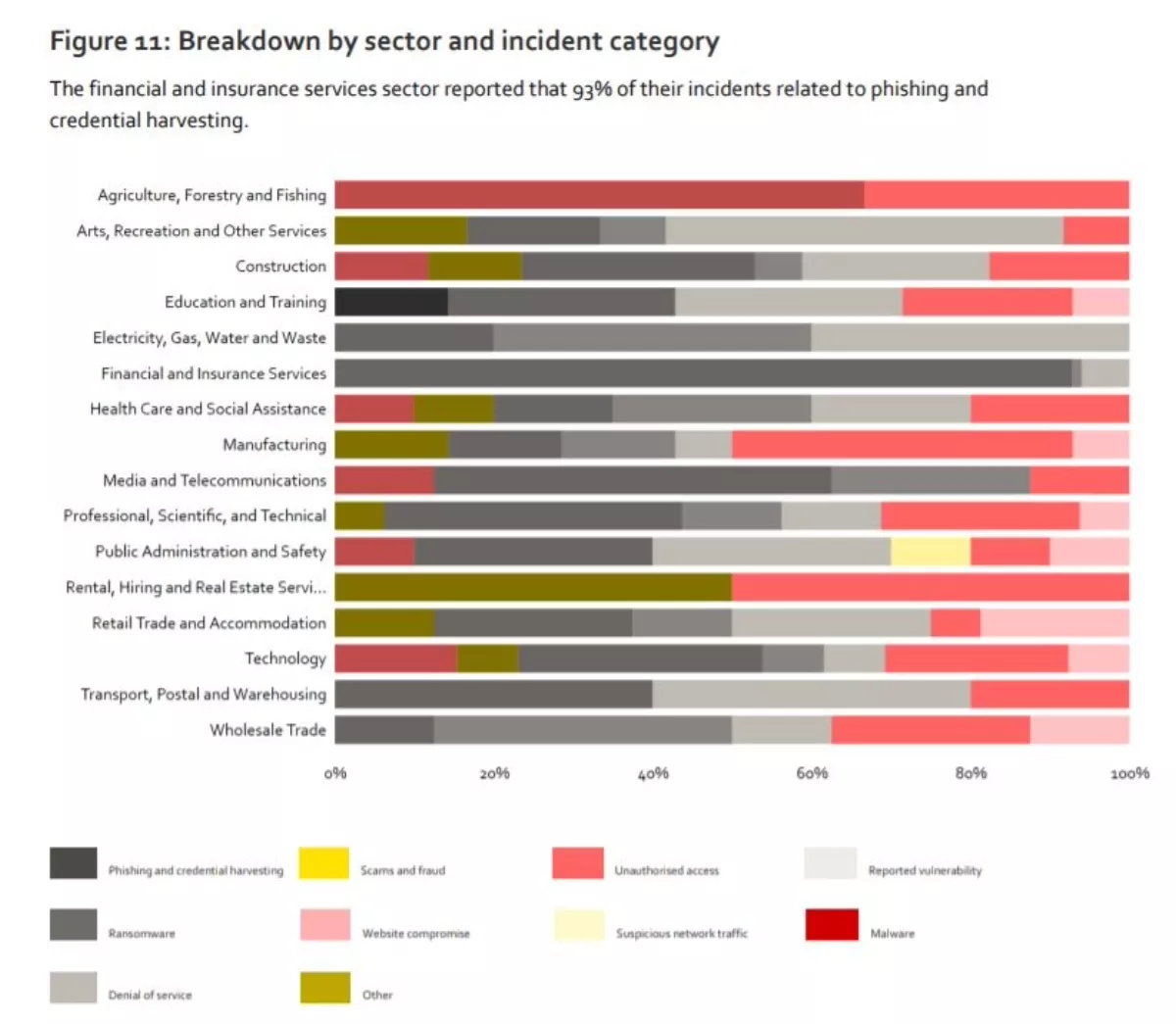
No business, no matter what sector they operate in, is immune. That's backed by solid research - CERT NZ's Q2, 2021 report breaks down cybersecurity incidents against businesses.
The report also breaks down incidents by sector. For example, ransomware incidents affected every industry. It was a similar story for unauthorised access and denial of service. Regardless of what type of incident you look at, every sector is affected by more than one type.
It is better to be prepared than to be caught off guard. So what is the best way to manage these kinds of issues? It's important first to understand how vendors provide security services and how businesses consume them. Some businesses may have a security-savvy team, enabling them to use products and services directly from a vendor and manage security in-house.
Other businesses like small and medium businesses (SMBs) may have fewer IT-savvy staff. As such, they may prefer to outsource their security through a managed service provider (MSP) or managed security services provider (MSSP) that has the expertise to do the job.
CCL head of information and security management, Gordon Greeff, says, "Small-medium businesses face challenges on a number of fronts, the biggest being access to skilled and experienced people. Businesses struggle to justify employing full time security professionals over and above general IT staff already on the payroll. And this is partly why much of the local security talent pool gravitates towards MSSPs."
Greeff adds, "Cybersecurity is also something that needs attention 24x7. MSSPs generally have the human resources and smart systems to run 24x7 operations. Smaller businesses do not. Consuming these capabilities and other managed security services from a common platform gives small-medium businesses access to protection that would otherwise only be available to much larger organisations.
Whether businesses self-manage their cybersecurity or recruit expert providers who can manage things for them, the bottom line is that security can't be ignored for the sake of their business - and their customers.
Advantage is another manage services provider that specialises in looking after cybersecurity for businesses large and small. Advantage's Auckland manager, Steve Smith, says that good security practices are not just limited to large enterprises.
"We are seeing a shift - the standard used to be that MSPs and MSSPs were utilised by SMBs for due to the lack of inhouse skill but there has recent shift. Due to lack of skills and available resources in New Zealand, we have noticed a trend of larger businesses engaging with MSSPs to look after security practices."
So if businesses get their cybersecurity right, that addresses part of the issue. The other part is how individuals take responsibility for their own data security.
As part of Cyber Smart Week, CERT NZ encourages New Zealand businesses and individuals to make simple changes.
1. Upsize and strengthen passwords
Passwords should be long and strong. In theory, anyway. CERT NZ recommends passphrases, strings of four words of longer and stronger than random letters, numbers, or symbols.
But there may be one barrier: How many times have you signed up for an account only to be told that your password of choice was too long? It's a frustrating setback in password security best practices. However, it also gives you a clue about which businesses keep on top of security - any business that allows people to create an account with a five-character password probably should not be trusted to secure your data.
Some businesses like Microsoft are doing their best to phase out passwords in favour of other methods like its own authenticator app, but look beyond the leading-edge tech firms, and you'll find that passwords remain the only option.
Public services like Inland Revenue's MyIR go as far as integrating RealMe as a login option, but try to buy your groceries from one of New Zealand's main supermarket chains, and you'll quickly find that passwords are your only option.
CERT NZ says businesses should also change default usernames passwords on hardware and software.
2. Enable two-factor or multi-factor authentication
Two-factor authentication (2FA) supplements logins by asking people for an additional piece of information when they log in (for example, an additional code sent via text or email, or via biometric security like a fingerprint). Businesses should offer 2FA to verify that people logging into their systems are who they say they are.
3. Update all apps and devices
Old devices and old software are prone to bugs and security risks if they are not updated. CERT NZ designed this advice primarily for consumers, but the same applies to businesses.
"When a company releases an update for an app or operating system it could mean attackers are already trying to exploit weaknesses, so you need to act quickly. CERT NZ recommends setting updates to happen automatically whenever a new version is available."
4. Uphold privacy
For businesses, this means collecting only the information needed to provide the product or service. For consumers, this means only providing the necessary information.
Businesses are bound by the 13 privacy principles as set out in the Privacy Act 2020. For example, principle 5 states, "You must make sure that there are reasonable security safeguards in place to prevent loss, misuse or disclosure of personal information. This includes limits on employee browsing of other people's information."
In other words, businesses need to protect all data they collect. CERT NZ also offers this advice for individuals, posing the question of whether it's really necessary to provide every little detail someone asks for, particularly when requests may not be legitimate.
"If a company or business asks you for information, think about why they might need it. Do they really need your middle name and phone number? If you're not sure, don't provide the information."
Trust plays a major part in customer loyalty. If customers don't believe a business keeps their data secure or uses it in the correct way, it is likely that customers will go elsewhere.
Cyber Smart Week encourages businesses and individuals alike to ask, 'what do I need to update, and more can I do to improve my cybersecurity'? They are questions that should not go unanswered.