Cryptominers posing a new threat for enterprise IT infrastructures
As well as viruses, trojans, worms and ransomware attacks, IT managers now have a new threat to worry about: cryptominers.
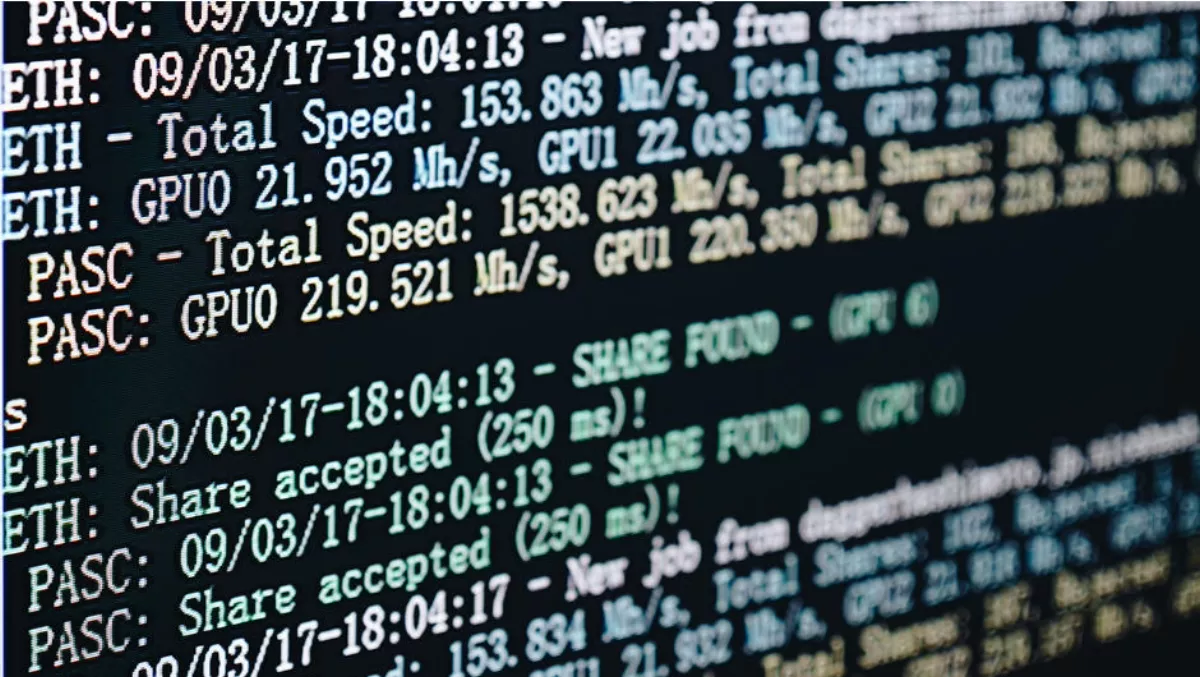
Following the massive spike in the price of Bitcoin in late 2017 and the associated flurry of public interest, attention has focused on the cryptomining used to create virtual currencies. Cryptomining is the process by which transactions are verified and added to a blockchain as well as the means through which new coins are created.
While many miners invest in powerful hardware designed for this task, others are taking a different strategy. Web-based methods allow website operators to use scripts to mine cryptocurrency within a browser, using the resources of a website visitor. In this way, it becomes possible to mine cryptocurrency without running a dedicated application on a computer owned or controlled by the miner.
The rise of the cryptominer
With interest in cryptocurrencies continuing to grow, there has been a noticeable increase in the volume of cryptomining transactions. During the past six months, Zscaler blocked more than 2.5 billion cryptomining attempts.
There are two key reasons for this dramatic rise. Firstly, following the Bitcoin price spike, legitimate sites are adopting cryptomining as an alternative source of revenue over traditional online advertising. These sites offer visitors a choice between seeing ads or being mined in order to view content.
Secondly, cybercriminals are also taking advantage of the trend by injecting JavaScript code into compromised legitimate sites to conduct cryptomining activities unbeknownst to site owners or visitors. In some cases, malicious advertisements are being leveraged for browser-based cryptomining activities. Finding a target
Traffic analysis shows that the category of domains used most for browser-based cryptomining activity include nudity and pornography websites followed by streaming media. The browsing time for users on video streaming sites tends to be higher than average, allowing miners to maximise their activity as visitors view movies or play games. Interestingly, websites of professional services and marketing organisations also ranked highly. This demonstrates the prevalence of mining activity within corporate networks.
Enterprise IT infrastructures are being directly affected by the trend in a number of ways. The CPU cycles caused by unwanted and unidentified mining activity result in increased wear and tear on corporate hardware. It also hogs corporate network bandwidth and causes performance issues.
Top five
There are five primary cryptominer tools currently in use. They are:
- CoinHive: This tool dominates the cryptominer market and represents the vast majority of cryptominers in the enterprise traffic scanned by Zscaler
- Crypto-Loot: This web-based miner is gaining popularity among attackers and malicious website owners
- JSE-Coin: This crypto-miner differs technically from other miners as involves the embedding of an external JavaScript file into a website
- DeepMiner: This is a free, open source JavaScript library for mining XMR (Monero) or ETN (Electroneum) cryptocurrency and the library can be embedded in a website
- Minr: This tool currently has relatively low adoption rates compared with the others and requires a website developer to provide an API for access.
Future developments
Analysis of web traffic shows cryptomining is increasing exponentially in popularity. However the practice, whether undertaken with permission or not, raises many questions when it comes to ethics and compliance.
Organisations that unknowingly have cryptomining activities taking place on their networks may be at risk of compliance violations if it is discovered that there are unidentified activities taking place on company systems.
At the same time there are also ethical questions such as whether or not site owners who have granted permission for their site to be cryptomined are responsible for notifying and educating site visitors on how their systems will be affected by this activity. Regardless of the answer, both enterprises and consumers suffer the same effects of cryptomining, including added CPU cycles, increased power use, and hardware erosion.
There is also an increased risk of exposure to malware due to the use of JavaScript by many cryptominer tools. Once injected into a site, JavaScript code can be easily manipulated by a cybercriminal for other uses, potentially exposing consumers and employees in enterprises to other harmful attacks.
To further complicate the situation, there is no clarity around regulation and disclosure requirements when it comes to cryptomining. While this will happen, it's likely to take governments some time to come to terms with the trend and its implications.
While organisations need to be aware of the implications of cryptomining, individuals should also ensure they are prepared for any unwanted activity. It is important to constantly watch out for a sudden spike in memory use that causes the PC to become slow and only allow JavaScript to run when visiting trusted websites.
Cryptomining is going to continue to grow rapidly and so awareness and preparation is vital. Take the time to ensure your organisation is ready for this new threat.

