Enterprise security stories - Page 30
.webp)
Genetec sets privacy rules for physical security data
Tue, 27th Jan 2026
#
data protection
#
smart cities
#
surveillance
Genetec issues privacy rules for physical security data, urging clear limits, encryption and ongoing cyber defence for surveillance systems.

Keeper brings zero-trust access governance to Slack
Mon, 26th Jan 2026
#
hybrid cloud
#
digital transformation
#
encryption
Keeper rolls out a zero-trust Slack integration, turning chat-based approvals into governed workflows while keeping enforcement in Keeper Vault.
Okta warns of real-time vishing kits defeating MFA
Mon, 26th Jan 2026
#
mfa
#
crypto
#
physical security
Okta warns new real-time vishing kits can hijack browser sessions during calls, tricking users into defeating non‑phishing‑resistant MFA.
.webp)
UK bill accelerates shift to offensive cyber security
Sat, 24th Jan 2026
#
firewalls
#
endpoint protection
#
devops
New UK cyber bill pushes critical sectors towards continuous offensive security testing as state-backed and criminal threats intensify.
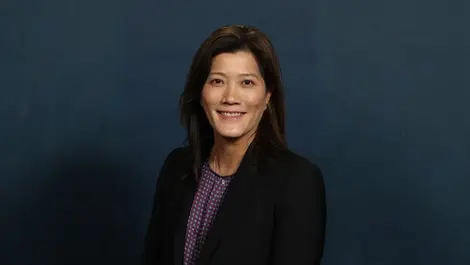
Cyderes names Lana Knop Chief Product Officer for AI push
Sat, 24th Jan 2026
#
saas
#
siem
#
digital transformation
Cyderes appoints Lana Knop as Chief Product Officer to steer post‑Lucidum product strategy and drive a new wave of AI‑powered security services.

CrowdStrike gains ISO AI governance boost for Falcon
Sat, 24th Jan 2026
#
socs
#
ai security
#
risk & compliance
CrowdStrike secures ISO 42001 AI governance certification for its Falcon platform, signalling audited, matured controls over its security AI.

Check Point unveils AI-ready continuous exposure management
Sat, 24th Jan 2026
#
firewalls
#
network security
#
cloud security
Check Point launches AI-ready Exposure Management to plug remediation gaps, unifying threat intelligence, prioritisation and automated fixes.

NCC Group, Delinea partner on managed PAM for AI era
Fri, 23rd Jan 2026
#
devops
#
hybrid cloud
#
digital transformation
NCC Group and Delinea launch managed privileged access service, targeting AI-era identity threats with Zero Trust, cloud-native controls.

SonicWall pushes unified automation for faster cyber defence
Fri, 23rd Jan 2026
#
malware
#
firewalls
#
ransomware
SonicWall launches unified automation tools to cut alert fatigue, speed cyber threat remediation and streamline overstretched security teams.

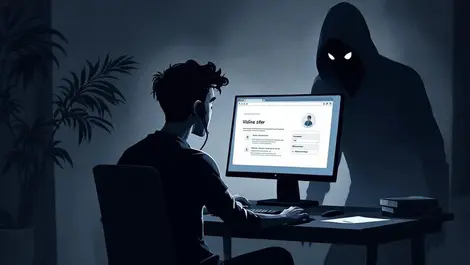
Phishing campaign exploits RMM tools for stealthy access
Fri, 23rd Jan 2026
#
firewalls
#
network security
#
phishing
Phishing campaign uses stolen logins and trusted RMM tools like GoTo Resolve and LogMeIn to quietly maintain access to corporate systems.

Cohesity boosts identity resilience for hybrid AD, Entra
Fri, 23rd Jan 2026
#
data protection
#
dr
#
ransomware
Cohesity has expanded its Identity Resilience tools to detect, block and rapidly undo attacks on hybrid Active Directory and Entra ID.

Radware unveils cloud service for unified API security
Fri, 23rd Jan 2026
#
firewalls
#
hybrid cloud
#
digital transformation
Radware launches cloud-based API Security Service unifying discovery, posture management and runtime defence to counter evolving API threats.

WitFoo shifts global cyber defence base to New Zealand
Fri, 23rd Jan 2026
#
siem
#
data science
#
socs
US cyber security firm WitFoo shifts its global base to New Zealand, making the country the launch pad for its “Cyber Grid” defence model.

Misconfigured cloud training labs open paths to attacks
Fri, 23rd Jan 2026
#
firewalls
#
hyperscale
#
cloud security
Misconfigured cloud training labs on AWS, Google Cloud and Azure expose major firms to live attacks via overly permissive access roles.

CrowdStrike secures ISO 42001 AI governance standard
Fri, 23rd Jan 2026
#
malware
#
cloud security
#
phishing
CrowdStrike earns ISO 42001 AI governance certification for its Falcon platform, touting independently audited, responsible AI controls.

Industrial AI drives new approach to OT cyber security
Thu, 22nd Jan 2026
#
firewalls
#
cloud security
#
iot security
Industrial AI and IT/OT convergence are forcing factories to abandon closed networks and adopt hybrid, zero trust cyber security architectures.
.webp)
KYND: big firms leave critical cyber flaws unpatched
Thu, 22nd Jan 2026
#
malware
#
application security
#
cybersecurity
Major firms are leaving known, actively exploited cyber flaws unpatched for six months or more, sharply heightening breach risks.

Legacy PKI blamed for outages & rising security risk
Thu, 22nd Jan 2026
#
encryption
#
cloud security
#
iam
Legacy PKI and manual certificate management are driving outages and security exploits as machine identities surge, CyberArk research warns.

Keeper adds instant account switching & passkey upgrades
Thu, 22nd Jan 2026
#
pam
#
mfa
#
mdm
Keeper rolls out instant multi-account switching and expanded passkey support across mobile and browser to streamline secure access.

AI reshapes data privacy risk across Australia, NZ
Thu, 22nd Jan 2026
#
data protection
#
devops
#
hybrid cloud
AI is reshaping data privacy in Australia and New Zealand, exposing shadow tools, privilege sprawl and weak identity controls, experts warn.