
It doesn't take some people long to abuse people's kindness and generosity in a time of mourning. Unfortunately scammers have been quick to harvest their own selfish opportunities after last week's shootings in Christchurch.
CERT NZ and Westpac have both issued alerts warning people to be on the lookout for email donation scams in the wake of the tragedy.
CERT NZ says that it has received numerous reports of scams and attacks, including online donation fraud, malware in video files, New Zealand websites defaced, and denial-of-service reports.
Online donation fraud is being conducted through phishing emails that include links to fake online banking logins. The emails also contain fraudulent bank accounts to which the scammers ask for donations.
Westpac has posted an example of one such email. “The scammers are sending out an email that carries Westpac branding,” the company says.
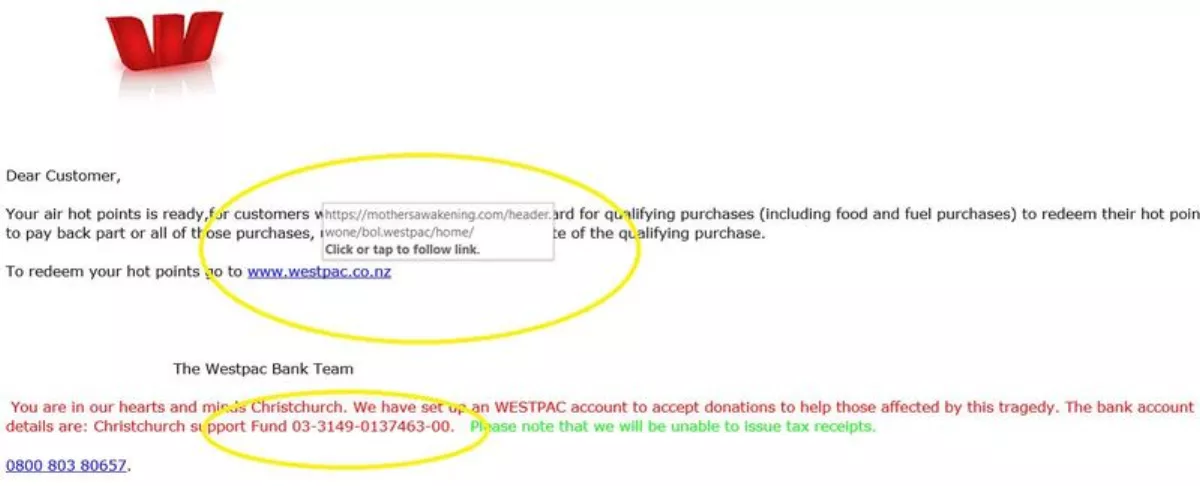
“Customers can identify the scam by hovering over the link in the email – they will see the link will take them to a website called mothersawakening. We ask anyone who receives this email to forward it to phishing@westpac.co.nz.
For those who want to make genuine donations, the Christchurch Foundation's Our People, Our City Fund has been set up. Donations can be made at most banks nationwide or by bank transfer to account number 15-3976-0091104-80.
CERT NZ also outlines that videos containing footage related to the shootings may contain malware. The malware is embedded in the footage and is being shared across compromised websites, as well as social media.
Some reports also note that attackers are defacing New Zealand website to spread political messages about the Christchurch tragedy. In some cases, some New Zealand websites are receiving threats about denial-of-service attack, which would take the websites offline.
The Government Communications Security Bureau (GCSB)'s director-general Andrew Hampton has also posted a statement saying that the GCSB had not “collected or received from partners any relevant intelligence ahead of the terrorist attacks”.
“New Zealand's intelligence and security agencies do not currently have the legal authority, technical means or resources to actively monitor all online activity that occurs in New Zealand. In addition, all intelligence and security agencies are grappling with the challenges of encryption and closed online communities,” Hampton says.
“GCSB has stood up a 24 hour operation response team which is working with domestic agencies and foreign partners to support Police and NZSIS.
“It is important that there will be the inquiry and GCSB is committed to providing all necessary support. It is of the utmost importance that the public are assured that GCSB acted lawfully and appropriately.
“Due to our focus on supporting the ongoing Police investigation and the inquiry I do not intend to comment further at this time.
CERT NZ advises the following:
“If you receive a phishing email or have found a website hosting political messages, report it to CERT NZ.
“If your website has been taken over with political content relating to the tragic events in Christchurch, report it to CERT NZ. We recommend you consent to share your report with our partner agencies (in this case, DIA and NZ Police).
“The Department of Internal Affairs considers the footage related to the attack as objectionable material, and therefore considered an offence to possess, share and/or host the harmful content. If you are aware of online footage related to the attack report it to the Department of Internal Affairs.
If you need to talk to someone, the following free helplines operate 24/7:
• Depression helpline: 0800 111 757
• Lifeline: 0800 543 354
• Need to talk? Call or text 1737
• Samaritans: 0800 726 666
• Youthline: 0800 376 633 or text 234
