
Essential tools for managing user identity and how they impact your bottom line
Customer identity and access management (CIAM) is how companies give their end-users access to their digital properties, as well as how they govern, collect, analyse, and securely store data for those users.
CIAM sits at the intersection of convenience, privacy, and security, providing a frictionless way for users to onboard and login is critical for driving conversions and building customer loyalty.
Protecting sensitive data from malicious intrusion and taking steps to prevent data breaches is central to a sound security policy and compliance with data privacy laws. Compiling user data into a single source of truth is essential to understanding an organisation's customers.
Given CIAM's complexity and dynamism, many organisations choose to engage a third-party Identity-as-a-Service (IDaaS) provider rather than build a solution in-house.
Essential elements of CIAM
Organisations need identity and access management (IAM) solutions for several classes of end-users: employees, business partners, and consumers. But each type of user requires a different balance of security and user experience (UX). CIAM solutions provide a unique set of features distinct from B2B or workforce identity solutions. They are:
Scalability
Unlike workforce identity solutions that support thousands of employees and vendors who require relatively static access to a pre-assigned list of applications, CIAM has to scale to millions and even billions of users. Scalability is a unique element of CIAM that requires third-party, cloud-scale stability.
Single sign-on
Single sign-on (SSO) allows users to log in to one application and automatically be logged into a set of other applications. The most widely known SSO example is Google G Suite, where logging into Gmail means users are automatically logged into YouTube, Google Drive, and other Google platforms.
SSO is a fundamental element of federated identity, and there are SSO options for B2B and workforce IAM solutions. The type of SSO designed explicitly for end-users is social login, which allows users to verify their identity with their credentials from a separate provider, like Facebook, Google, or Apple.
Social logins greatly simplify the registration process for users, leading to increased conversions and fewer customers abandoning their shopping carts.
Multi-factor authentication
Multi-factor authentication (MFA) is a more secure means of authenticating user identity than the traditional username/password combination. Passwords are easy for hackers to steal or guess, so MFA demands an extra credential for users to prove their identity, such as a one-time PIN or a biometric credential.
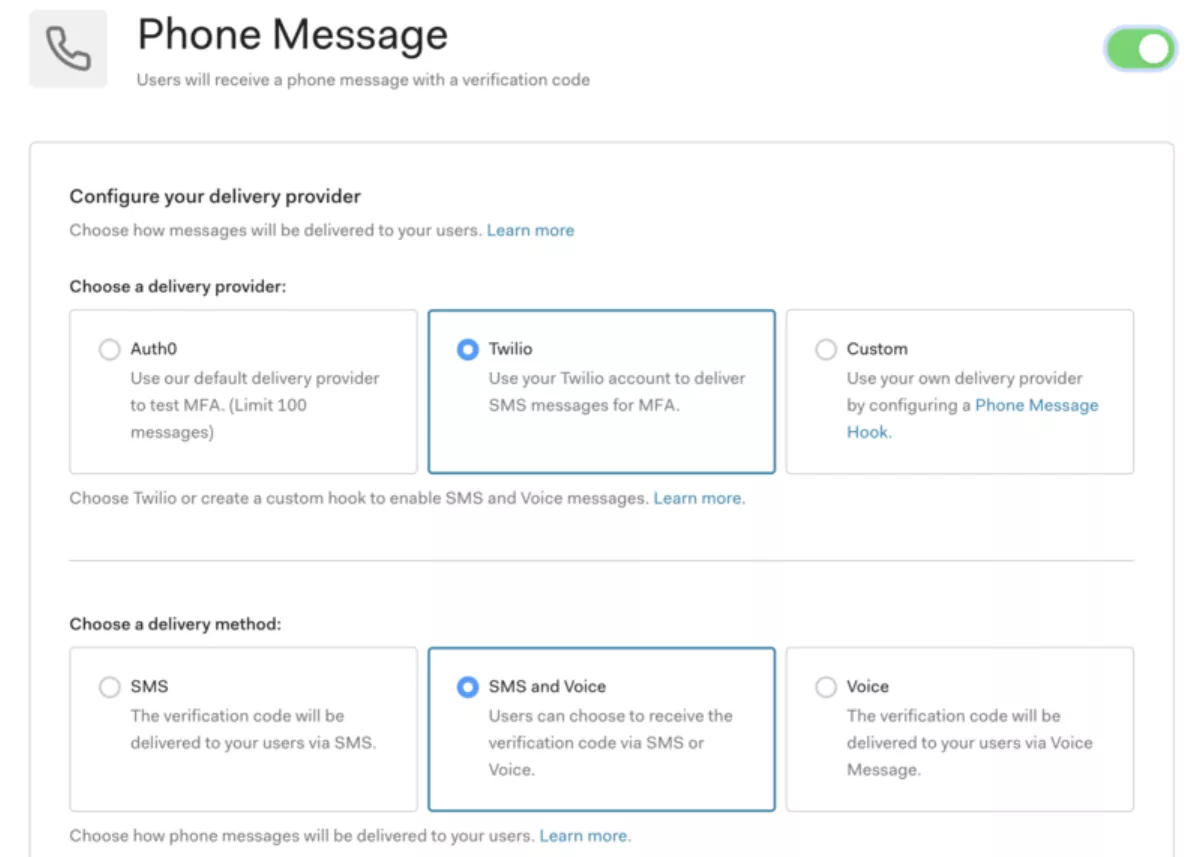
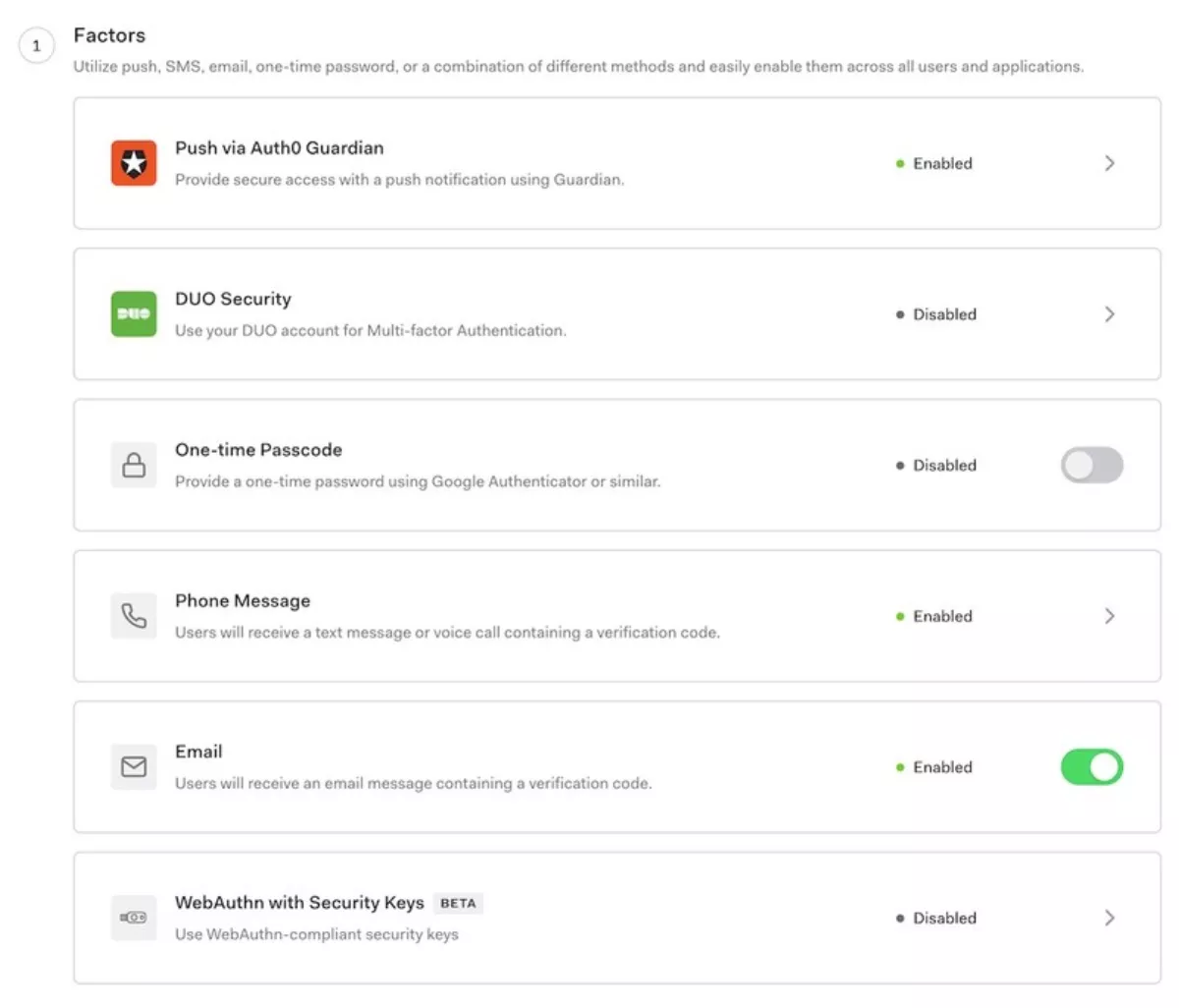

MFA is increasingly regarded as a basic requirement for security. However, it's critical to implement MFA for end-users in a way that doesn't introduce unnecessary friction.
MFA should only be triggered based on the assessed risk, such as when a customer signs in with a new device or makes a suspicious transaction.
Centralised user management
A CIAM solution helps achieve centralised, data-rich customer profiles that function as a single source of truth about users.
The single view of customers is an advantage for analytics, but it also helps companies meet the reporting requirements of data privacy laws because all profile data is accessible and portable. Knowledge about the user is also critical for building more personalised experiences, which drives higher retention rates.
CIAM Is central to data security
A robust CIAM solution has security features to protect against fraud, hacks, and misused data on multiple fronts.
In recent years, the login box has become the front line for fending off intruders. One of the most damaging forms of broken authentication attacks is credential stuffing, in which hackers use passwords stolen in one breach to break into other sites. This method works given people's tendencies to reuse passwords. Credential stuffing attacks alone cost businesses an average of US$4 million a year, according to a 2019 study from the Ponemon Institute.
The best defence against credential stuffing and other authentication-based attacks is a CIAM solution with MFA and brute force protection. Brute force protection stops hackers from flooding applications with login attempts and crashing sites, while MFA ensures that a stolen credential won't give hackers automatic access to users' accounts.
CIAM systems also help protect customer data from back-end mischief in the event of a data breach or hack.
CIAM helps manage data privacy law compliance
Data privacy laws like GDPR and CCPA fundamentally rewrite the rules for how organisations collect, store, and share personal data. In Australia, the Privacy Act 1988 provides the 'Australian Privacy Principles' with rules about transparency, direct marketing, and personal information security.
Centralised user management is essential in fulfilling the reporting and erasure requirements of data privacy laws.
Data privacy laws are all about controlling who can access personal data, so encrypting customer data and controlling access to it are baseline requirements. A CIAM solution needs to provide all of these elements, as well as tailoring data collection and consent management practices to the relevant laws.
CIAM is a business enabler through customer experience and convenience
With the right approach to CIAM, customers can experience easy logins and receive services based on a nuanced understanding of their needs.
Social logins provide users with a friction-free registration experience without having to remember another password. Businesses benefit from shared knowledge with that social media provider, so they automatically know customers' location, timezone, language, and other details to guide upsell recommendations.
Studies have shown that reducing the number of form fields increases conversion rates. With social logins, organisations can eliminate the form altogether and enable one-click signup.
CIAM: a holistic approach to customer identity management
CIAM plays an increasingly central role in how companies create their digital identities and manage their customer relationships. Companies are allocating more resources to their access management solutions, either from day one or as part of a larger digital transformation, as an effective and impactful way to balance the three forces of convenience, security, and privacy.

